Biometric authentication methods, such as fingerprint scans or facial recognition, seem safe and secure. But it turns out it’s not quite that simple.
Why biometric methods seem more secure than using a PIN code
When you use a fingerprint or facial snapshot, it seems like only you and your unique biometrics can unlock your device, right? After all, it seems a lot more complicated than simply entering a numeric combination.
However, the magic didn’t get past the hackers. Here’s what they came up with an ingenious and insidious Android malware known as the Chameleon Trojan. This trojan is able to pretend to be a legitimate application, and very convincingly at that. It fraudulently obtains permission to access your smartphone, and then it’s inside like an uninvited guest at a party.
As soon as Chameleon gains access, it starts its work. Not only does the software track your activity, but it also captures your credentials. This includes bank details, passwords, and, of course, PINs.
So what is Chameleon banking Trojan? It is malware that specializes in stealing banking data and extorting information from your device. Its goal is to gain access to your financial world to stealthily siphon valuable data from there. The trojan can infiltrate your device through an insecure website, for example, if you like to visit dubious sites like twinspinCA in search of real money casinos.
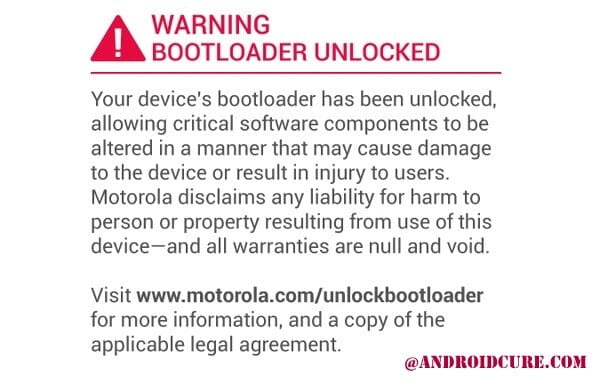
Various security measures have been introduced into the Android operating system in recent years, and one of the new ones introduced in version 13 of the OS is the “limited customization feature.” It’s designed to give users more control over which apps have access to certain settings and features on their devices. But as it turns out, hackers are always one step ahead.
According to information from BleepingComputer, the malware is able to use tricks to access a new limited customization feature without notifying users. This means that malware can request permission to use limited customization under the guise of legitimate requests or applications. Once it gains the right of access, the software takes full possession of all smartphone functions, including the ability to disable or bypass biometric authentication such as fingerprint scanning or facial recognition.
How to protect your phone
You’re probably wondering how to avoid this kind of trouble. In fact, there are several steps that can help reduce the risk of such incidents:
- Always keep an eye on the permissions that your apps request. If something seems suspicious, it’s better to refrain from granting permission and search for information about that app.
- It is important to update the operating system and apps on your device to minimize vulnerabilities.
- -Regularly pay attention to activity and transactions in banking apps to promptly detect unauthorized transactions.
Hackers are always looking to develop new methods of deception and malicious technologies, but being aware of these risks and taking extra precautions can go a long way in protecting your device and sensitive data.