There are more spyware programs for desktops than for cell phones. First, because computers have been with us for decades, while smartphones only started to become a mass phenomenon closer to the mid-2010s. Second, because desktop operating systems are more complex. That makes them more difficult to protect – there are more potential vulnerabilities. And there are a lot of reasons to think hard about security. Here are just a few examples of what spyware can do in the hands of attackers:
- Monitor your keystrokes on the keyboard. This way it’s possible to “spy” passwords from essential services and even a TonyBet login or messages you write to other people in emails and messengers.
- Create screenshots and video recordings of what is happening on the infected computer’s screen.
- Search for valuable information in the file system of a compromised PC: corporate documents, photos for blackmail, or, for example, documents where passwords to various services are written inconsiderately.
- Record audio with a microphone and video with the computer’s front camera if it’s a laptop.
- Spoof websites in order to collect your login data for various services or to divert payments to malefactors.
- Directly steal data: from any files from your computer’s data storage in general to individual things like documents you send to print.
- Gather information on system peculiarities and existing vulnerabilities for a deeper level attack or remote control of an infected computer.
How Spies Get Into Your Computer
It seems by now that everyone should remember not to click on dubious links, but this is still the most popular way for spyware to get onto users’ computers. From a chat window, an email or just a suspicious page, you get to a site that runs an executable file or a web app. And they are already doing their dirty work: installing malware in the system or browser. The download is likely to take place in stealth mode. And it can also be that the site will throw you silly banners, repulsing which you will certainly click somewhere, thus triggering the installation of bad software.
The second most popular way to catch spyware infection is by downloading some program at the first link in the search. You may even be lucky enough that what you are looking for will work, but you will almost certainly catch a whole zoo of viruses and spyware along with the necessary software. Exactly the same thing can happen with a program downloaded from a torrent tracker, although if you choose a popular old distribution at a big known site, the probability of an unfavorable outcome is greatly reduced.
On the third line of the “start a malware” hit parade are programs that are advertised as useful, but really are not: their main purpose is not to help you, but to become an entry point for viruses and spyware. You’ve probably seen banners calling to download “Internet speedup” software, “super-fast download manager”, “handy new search engine”, “ultimative disk cleaner” or something similar. That’s exactly it.
More often than not, the user is tricked into visiting an infected page, where malicious software is thrown at him. A less common but popular story is a planted USB flash drive with malware, which a person plugs into their computer to see what’s there.
How to Get Rid of Spyware
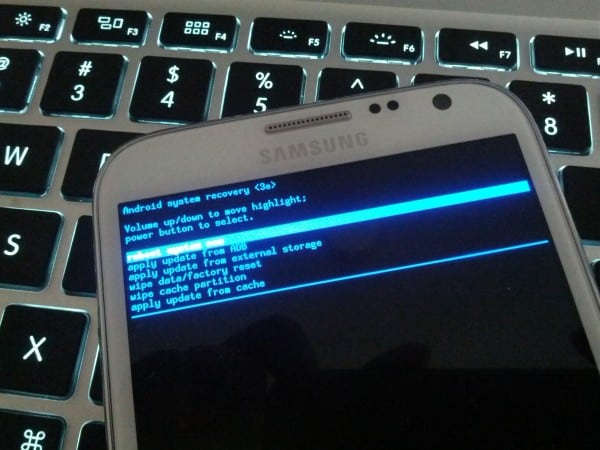
The most effective way to get rid of desktop spyware is to completely format the drive and reinstall the system from scratch. You can not restore from a backup, because it is very likely that the spyware has penetrated there as well. It is very important to be extremely careful with valuable data, which you want to save. When copying to an external HDD or SSD, sneaky viruses can “jump” there and then come back to the system. A good solution would be cloud services: if you temporarily transfer files there, their operator’s servers will certainly check them for the presence of bad software. And the protection there is serious: the chance of something slipping through is absolutely minimal.
If you continue to work in an infected system and use thumb drives and external drives, it’s extremely essential to connect them in read only mode. This is the only way to make sure they do not become an instrument of further malware distribution.
After reinstalling the system do not forget to change all passwords, and just in case it can be done from another, definitely not infected PC, in case some traces of malware are left on yours. They should definitely be searched in a fresh system with a reliable anti-virus.